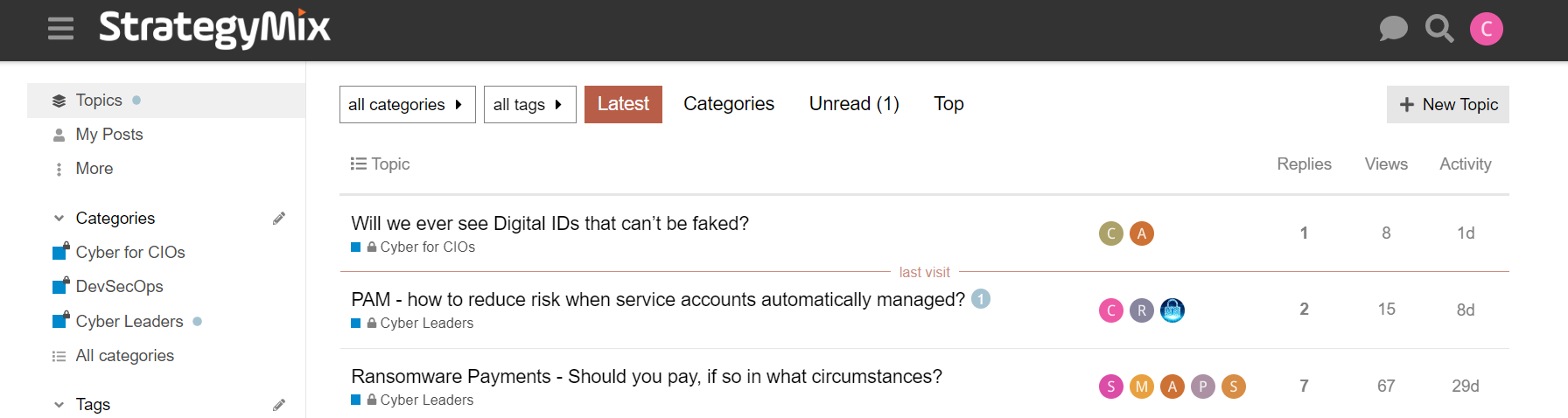
To visit the Insights Q&A Forum go to: https://insights.strategymix.com/
Insight Questions
About Insights
The StrategyMix Insights Online Forum operates in much the same way as our roundtables in the sense that they deploy a Q&A format and are run under the Chatham House Rule. The group is also tightly moderated, so there will be no spam - just quality content.
The group is only open to Senior IT Executives and to carefully screened Trusted Advisors, who we believe will add value by providing valuable answers to the forum questions.
Note: If you are already an Insights member, the link to logon is: https://insights.strategymix.com/
Exploring the Vulnerabilities of AI :A Universal Prompt Injection Attack in the GPT Store
Last Update: 01 Feb 2024 - (Cyber Leaders)
ASOC and ASPM Tools Is anyone looking at tools for application security orchestration and correlation (ASOC), application security posture mgt. (ASPM) and software supply chain security? Any recommendations? We are looking at ArmorCode, CyCode, Dazz, Legit Security, and Ox Security.
Last Update: 02 Nov 2023 - (Cyber Leaders)
What tools are you using to manage ISO 27001? We are evaluating options for implementing ISO27001. We believe we will need a tool to manage our documentation and testing of controls, manage risks and support the audit for our certification. We have seen tools which are just focussed on supporting tasks and documentation (I think of these as a vertical specific JIRA) and others which claim to integrate with our infrastructure and applications (eg: AWS and Salesforce) to “automatically” identify risks, controls and create incidents for review/remediation. Question: What system are you using to manage your ISO27001 or similar compliance? How integrated is it with your other systems?
Last Update: 31 Oct 2023 - (Cyber for CIOs)
How to maintain business buy in for cyber risk management? What has been the strategies used to maintain the business’s buy in and support for cyber risk management (in particular things like mandatory training) and how successful have they proven over time?
Last Update: 19 Oct 2023 - (Cyber for CIOs)
Which Managed Security Service Providers (MSSPs) have you used, and what was your experience of them? I’ve worked with a number of these, where they’ve provided SOC, threat intelligence and vulnerability management services. There are pros and cons to using them, for sure. Which MSSPs have you used, and what were your good and/or bad experiences?
Last Update: 12 Oct 2023 - (Cyber Leaders)
My question is about AI and is in 2 parts. How and where do you see AI being an integral part of a cyber defense strategy and how and where do you see AI being a Security risk and how will it be mitigated?
Last Update: 04 Oct 2023 - (Cyber Leaders)
Productivity metrics - do you use these? I’ll make an assumption that most companies are starting to struggle with productivity, especially with the upsurge in remote working or working from home. It seems that I hear this from many people across all industries. It’s important for CEOs and our executive team is wondering what is the best way to test this assumption, relying of course on the CIO to answer this. We use the Microsoft 365 stack, as I’m sure many others do as well in this forum. What tools do you leverage in M365 to help you answer these questions? How much time are people spending in online meetings? How many people are in these meetings? Does general work activity fluctuate when staff are working remotely vs. the office? Thanks in advance.
Last Update: 28 Sep 2023 - (Non-Cyber)
Cyber Frameworks - which would you recommend? We have been PCI compliant for a decade now and we have used PCI as a de facto cyber framework despite its limitations (it is very prescriptive and very narrow in scope). We want to adopt one of the broader frameworks (NIST, Essential 8 etc) while avoiding too much duplication and added work – does anyone have any recommendations or experiences to share in this area? We looked at this in panel discussion and there were some suggestions that NIST works best as a basis but the best answer may be a tailored mix. I like that (and I think it is always inevitable to some extent) but I do also like the certainty when interacting with partners, insurers and board of being able to state compliance to a particular framework. Any further thoughts?
Last Update: 28 Sep 2023 - (Cyber for CIOs)
Which frameworks and controls are companies using to defend against internal and external source code compromise and CI/CD pipeline compromise? Some context: I’m working with our head of DevOps on securing the global DevOps program. So, I’m focused on creating a custom framework for securing the “production line” of software developed in-house. I’m looking at OWASP’s DevSecOps maturity framework plus Gartner’s content (I have a sub). Both aren’t exactly what I’m looking for. My question: I’m interested to know which frameworks and controls companies are considering for securing repositories for source code, artifacts and containers, commits and CI/CD pipelines. We’re standardising on GitHub, including GH Advanced Security, and are looking at tools like Cycode and Legit Security.
Last Update: 26 Sep 2023 - (Cyber Leaders)
How are others handling threats like juice-jacking, or staff plugging in random USB drive/disk? What combination of approaches do you use?
Last Update: 13 Sep 2023 - (Cyber for CIOs)
